- Ledger’s Donjon crew exploited MediaTek telephones, recovering PINs and crypto pockets seed phrases
- Attackers can extract root cryptographic keys from switched-off Android units by way of USB
- Trustonic’s Trusted Execution Atmosphere fails to forestall assaults on one-quarter of Android units
Ledger’s white-hat hacking crew, the Donjon, found a vulnerability in MediaTek-powered Android smartphones which permits attackers to entry delicate knowledge in beneath a minute.
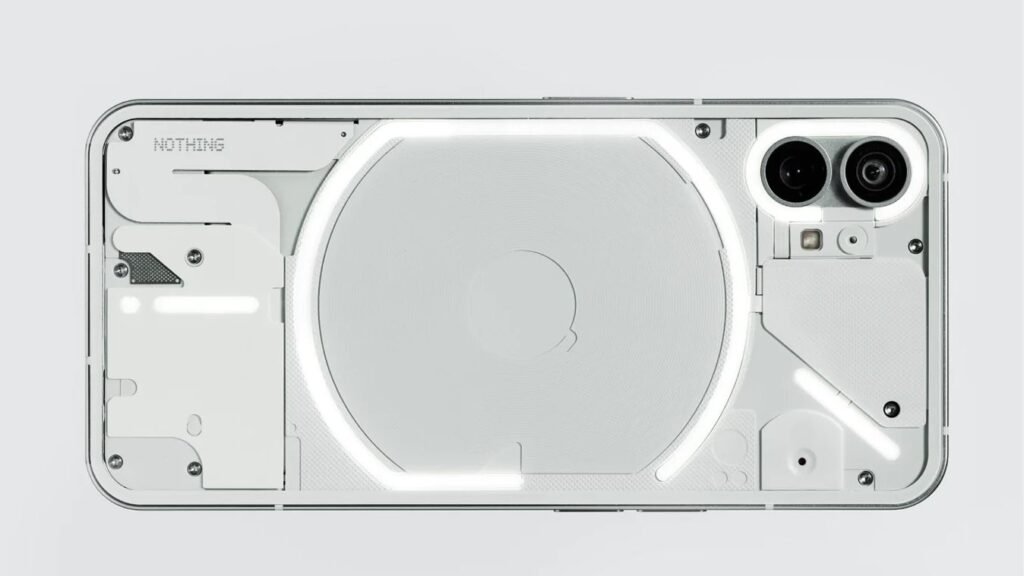
Utilizing a Nothing CMF Telephone 1, the Donjon bypassed the Android working system utterly, recovered the PIN, decrypted storage, and extracted seed phrases from a number of crypto wallets.
The flaw impacts units utilizing Trustonic’s Trusted Execution Atmosphere alongside MediaTek processors, present in roughly one in 4 Android smartphones worldwide.
Article continues under
You could like
Attackers can join a powered-down cellphone by means of USB and retrieve root cryptographic keys earlier than the working system hundreds.
As soon as obtained, these keys permit offline decryption of storage and brute-forcing of the machine PIN, exposing utility knowledge, together with messages, pictures, and pockets info.
Zero-click assaults reveal that Android smartphones continuously lack enough {hardware} and firmware protections to safe delicate consumer info towards superior exploits.
“This analysis proves what we’ve lengthy warned: smartphones had been by no means designed to be vaults. Whereas this may be patched, and we encourage all customers to replace with the most recent safety fixes,” stated Charles Guillemet, Chief Expertise Officer of Ledger.
“In case your crypto sits on a cellphone, it’s solely as protected because the weakest hyperlink in that cellphone’s {hardware}, firmware, or software program.”
The Donjon crew conducts common audits of Ledger’s units and third-party {hardware}, responsibly disclosing vulnerabilities to permit producers to subject fixes earlier than exploitation happens.
Ledger disclosed this vulnerability to MediaTek and Trustonic beneath the usual 90-day disclosure course of, offering time for safety patches to achieve affected OEMs.
What to learn subsequent
MediaTek confirmed it delivered updates to OEMs on January 5, 2026, and the vulnerability was publicly disclosed on March 2, 2026, as CVE-2025-20435.
Customers ought to instantly set up safety updates to mitigate potential assaults, as firmware able to being upgraded stays essential for patching zero-day exploits successfully.
This exploit reveals the dangers inherent in counting on cellular units to retailer personal knowledge, together with crypto wallets and different delicate info.
All knowledge saved on Android smartphones stays vulnerable to hardware-based assaults, emphasizing that quick patching is the one sensible protection towards superior threats.
Customers must be conscious that even trendy enterprise smartphones carry inherent safety dangers, and {hardware}, firmware, or software program flaws can expose delicate knowledge with out warning.
Delicate enterprise or private knowledge shouldn’t be thought-about safe on cell phones, and reliance on these units alone for storing belongings is inherently dangerous.
Comply with TechRadar on Google Information and add us as a most popular supply to get our skilled information, opinions, and opinion in your feeds. Be certain to click on the Comply with button!
And naturally you may as well comply with TechRadar on TikTok for information, opinions, unboxings in video type, and get common updates from us on WhatsApp too.