I known as my ISP final week a couple of flaky fiber connection, and midway by means of the decision, the rep casually learn out my router’s producer, firmware model, and each my Wi-Fi community names. I hadn’t informed them any of that. I sat there for a second attempting to determine how they knew, after which the uncomfortable follow-up query hit me: if they will see that, what else are they seeing? How far into my community does their view really attain?
This bought me intrigued, and after a little bit of digging, the router particulars turned out to be the least fascinating half. What stunned me was realizing that by default, each single web site I go to passes by means of my ISP’s DNS resolver in plaintext. Each lookup, each area, is tagged with my IP and a timestamp. I would been assuming HTTPS coated me. It would not. And the repair turned out to be one setting I would by no means bothered to examine on any of my PCs.
Your ISP can see each area you go to by default
The DNS layer is the weak hyperlink in your connection
Tashreef Shareef / MakeUseOfCredit: Tashreef Shareef / MakeUseOf
Each time you open a web site or launch an app, my cellphone or PC has to translate a site identify like youtube.com into an IP tackle. That translation is a DNS lookup, and by default, it goes straight to my ISP’s resolver within the clear. They see the timestamp, my public IP, and the precise hostname. Do this a couple of thousand occasions a day throughout each machine in the home, and also you get an in depth image.
What’s fascinating is how a lot that log reveals with out touching a single web page of content material. The gaps and spikes in DNS site visitors map out after I get up, after I sleep, and after I depart the home. The domains trace at my financial institution, my streaming providers, the well being websites I’ve checked, and each good machine on my community phoning house. It is not simply browser historical past, however each app on each machine, captured centrally, and most of the people by no means contact the default DNS their router fingers out.
HTTPS encrypts the web page, not the lookup
Why the padlock in your browser is not the total story
Tashreef Shareef / MakeUseOfCredit: Tashreef Shareef / MakeUseOf
Most individuals suppose the padlock icon in your browser was the top of the dialog. If a web site hundreds over HTTPS, the contents are encrypted, so my ISP cannot learn the web page I am on or the shape I am filling out. That half remains to be true. What I missed is that the DNS lookup occurs earlier than the encrypted connection even begins.
So whereas my ISP cannot see which particular video I watched or which article I learn, they will completely see that I contacted YouTube, a particular information web site, or a psychological well being useful resource. The hostname additionally tends to leak within the TLS handshake by means of a subject known as SNI, until each my browser and the positioning help a more moderen characteristic known as Encrypted ClientHello. Most do not but.
The top result’s that HTTPS alone offers me content material privateness, however not metadata privateness. My ISP would not have to learn the web page to construct a profile of my routine and pursuits, as a result of the domains already reveal sufficient.
An encrypted, filtering resolver fixes each issues
Swap the resolver, and the ISP goes darkish
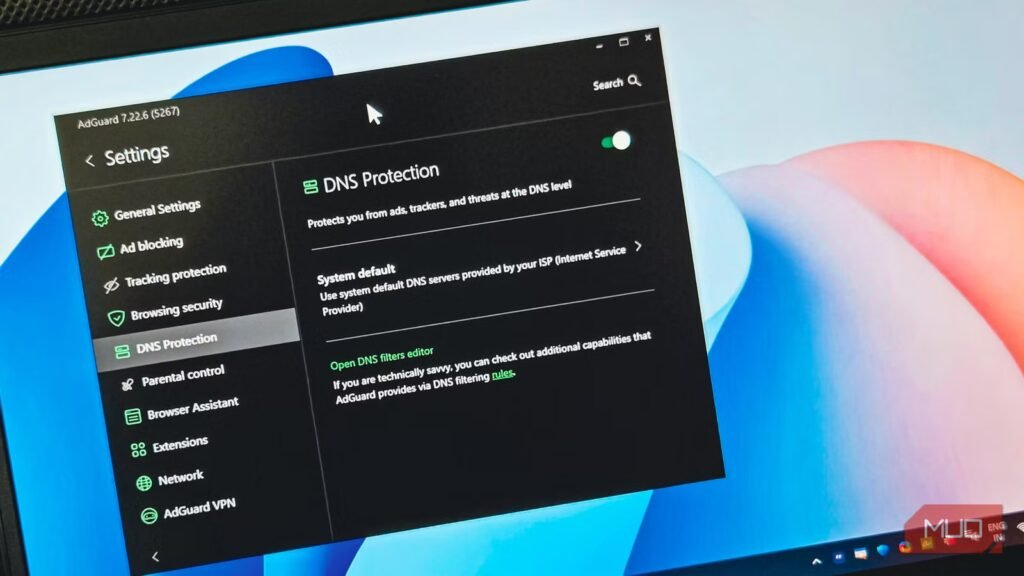
The repair is to cease utilizing my ISP’s DNS solely and route lookups by means of an encrypted resolver that additionally filters junk. As soon as queries are encrypted with DNS-over-TLS or DNS-over-HTTPS, my ISP sees an opaque stream to the resolver as a substitute of a readable record of domains. Filtering on high of that blocks advert servers, trackers, and identified malicious domains earlier than my units ever join.
The only path is a per-device setup. On Android, I switched my Personal DNS to dns.nextdns.io underneath Settings > Community & web > Personal DNS, which let me decide precisely what will get blocked by means of a dashboard. On Home windows, I pointed my adapter at Quad9 (9.9.9.9) after benchmarking it towards my ISP’s DNS and seeing it come out quicker and safer.
Now, if you need whole-home protection, the cleaner choice is to vary the DNS on the router stage so each machine, together with good TVs and IoT gear, inherits it mechanically. For this, you may go for an choice like NextDNS that provides granular management and parental filtering, which most free resolvers do not provide, and the free tier covers a traditional family.
DNS filtering has actual limits
What it could actually’t block, and the place it falls quick
Amir Bohlooli / MUO
I do not need to oversell this. DNS filtering is a big improve, but it surely nonetheless has its limitations.
The largest hole is same-domain advertisements. YouTube, Twitch, Netflix, Hulu, and TikTok all serve their advertisements from the identical area because the content material. A filter cannot block the advert with out breaking the entire service, so in-stream advertisements sail straight by means of. Browser-based advert blockers nonetheless matter for that sort of site visitors.
Some units additionally ignore no matter DNS you set. As an illustration, Chromecast, Android TV bins, and sure good TVs hardcode Google or Cloudflare DNS and silently bypass my router settings. The one dependable repair is obstructing these hardcoded IPs on the firewall, which most client routers do not make simple.
Lastly, encrypted DNS is not a VPN. Even with lookups hidden, my ISP can nonetheless see the vacation spot IPs my units hook up with and, typically, the SNI hostname within the handshake. For full metadata privateness, I would want a VPN or Tor on high. DNS filtering simply closes the most important and best leak.
Your ISP would not have to know your looking habits
My present setup is NextDNS on the router for the entire home, plus Quad9 on units that journey with me. This mixture offers filtering throughout each gadget at house, a privacy-focused fallback after I’m on cellular knowledge, and roughly zero ongoing upkeep. It is the closest factor to a set-and-forget privateness improve I’ve discovered.