I’ve observed from expertise that when my Linux packages fail, it is usually a delicate occasion that may go away you confused or not sure of what really went unsuitable. When I’ve fallen again to prime, htop, and even the extra most popular iotop, one of the best I get is information referring to CPU and reminiscence utilization, with no actual perception into what the failing course of is definitely doing.
At such instances, it is not sufficient to know that one thing is unsuitable. I often wish to see why. The strace -p command has made an actual distinction. As soon as I connect it to a working course of, it exhibits each name that course of makes.
See what a course of is doing in actual time
Attaching strace and studying the primary traces of output
If you actually need to know strace, you simply have to make use of it. It is an observability device, however fairly completely different from inotifywait. Connect it to a working course of utilizing this format: sudo strace -p . And if you do not have the PID, any of the instructions under will assist you to discover it. I exploit Firefox within the examples:
pidof firefox
pgrep -a firefox
ps aux | grep firefox
The strace -p command nearly immediately begins to provide outcomes, and working it on an precise Firefox course of can produce this outcome:
epoll_wait(5, [], 1024, 999) = 0
futex(0x7f3a2c0, FUTEX_WAIT, 1, NULL) = 0
openat(AT_FDCWD, “/proc/self/maps”, O_RDONLY) = 7
learn(7, “…”, 4096) = 4096
Every line exhibits a name identify first, then its arguments, and at last a return worth. The traces characterize requests Firefox makes to the kernel. From the above outcome, this is what I deduce:
- epoll_wait(…) = 0: The method is ready for an occasion, however nothing has arrived.
- futex(…) = 0: The method is coordinating between threads.
- openat(…) = 7: After the method opened a file, it acquired file descriptor 7 again.
- learn(…) = 4096: The method learn 4096 bytes from that file.
In case your output is continually altering, it tells you that the method is energetic. Error returns reminiscent of ENOENT or EACCES point out file errors; repeated epoll_wait or ballot calls with no progress point out the method is idle and ready. After analyzing the method, utilizing Ctrl + C will cleanly detach strace.
Add the -f flag to get outcomes from threads and youngster processes. This may be helpful for monitoring browsers and bundle managers.
What strace is definitely displaying you
Understanding syscalls with out getting misplaced in concept
Afam Onyimadu / MUO
A program’s actions usually undergo the kernel. These can embrace file opening, community requests, or reminiscence allocation. For the reason that program can’t carry out these duties straight, it should make system calls that enable the kernel to execute them.
strace can print all these calls as a result of it operates between the applying and the kernel. Its place makes it correct. Quite than inferring, it is displaying you precisely how this system asks the system to execute an motion. Main classes usually appear to be this:
Class
Widespread syscalls
What you are seeing
File I/O
openat, learn, write
App studying or writing configuration recordsdata
Community
join, recvfrom, sendto
App speaking with a server or socket
Course of
clone, execve
App spawning subprocesses
Reminiscence
mmap, brk
App allocating or releasing reminiscence
Ready
ballot, epoll_wait, choose
App idle, ready for an exterior occasion
Thread sync
futex
Threads coordinating with one another
strace does not present supply code or software logic, however these aren’t at all times the defining parts for locating what’s damaged. It exhibits what a program does on the system degree, which will be extra vital for troubleshooting what’s damaged.
It makes use of ptrace, which is analogous to the mechanism gdb and different debuggers use, and typically requires sudo to run.
Associated
Linux has a built-in crash restoration trick, and extra folks ought to use it
Make your Linux system reboot itself and repair crashes routinely.
Making strace output helpful
Filtering noise so the issue turns into apparent
Afam Onyimadu / MUO
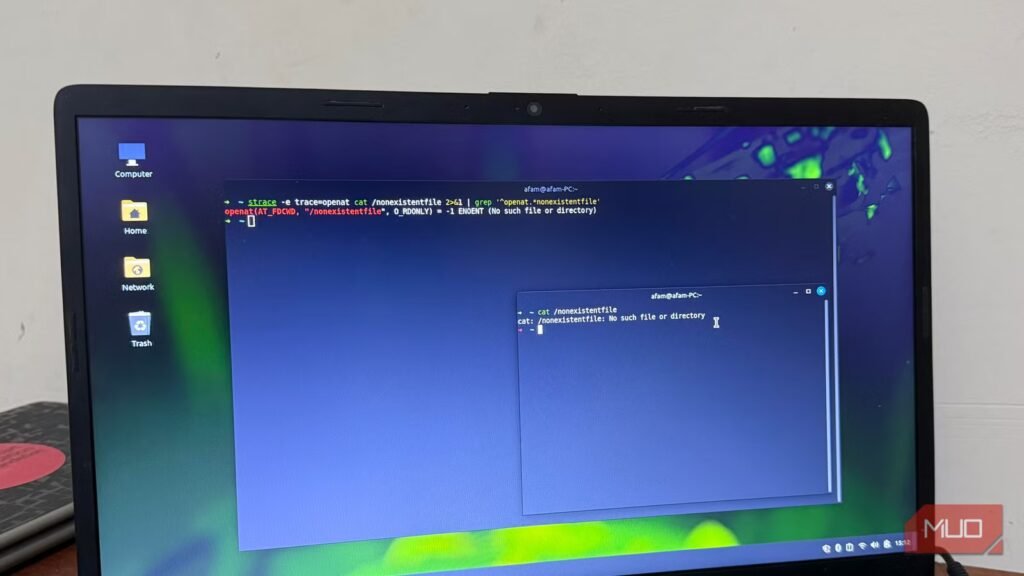
If the method is busy, it’s possible you’ll not be capable to learn the uncooked strace output due to how briskly it strikes. Narrowing outcomes down even earlier than they seem on the display screen will assist. You possibly can obtain this both through the use of the built-in class filters or by piping to grep. The precise choice to go along with will depend on the precise downside.
Listed below are just a few examples:
File concern — app cannot discover or open one thing:
strace -p -e hint=file 2>&1 | grep “openat|ENOENT”
On this case, I embrace 2>&1 as a result of it redirects stderr to stdout, so the pipe sees strace output. It offers the pipe one thing to work with and exposes solely file-related calls, making certain failed open makes an attempt get instantly surfaced by ENOENT (file not discovered).
Community concern — app failing to attach:
strace -p -e hint=community 2>&1 | grep “join|ECONNREFUSED|ETIMEDOUT”
The above command reveals the precise ports and hosts the app targets. It signifies if requests are being refused or timing out.
Caught app — determining why nothing is going on:
strace -p 2>&1 | grep “futex|ballot|epoll_wait|nanosleep”
With out strace, processes blocked on epoll_wait and people blocked on a futex timeout can seem similar to different instruments. Nonetheless, none of those is similar as crashing.
With completely different patterns, you need to know what to search for. The information under will assist:
Output sample
What it means
ENOENT on openat
File or path does not exist
EACCES on openat
File exists however course of lacks learn permission
ECONNREFUSED on join
Goal port is closed or service is not working
ETIMEDOUT on join
Host is unreachable or firewall is dropping packets
epoll_wait / ballot with no return
Course of is idle, ready on I/O or a shopper
futex blocking for a very long time
Thread is ready on a lock held by one other thread
learn(0, …) with no return
Course of is ready on stdin—it wants person enter
What I discovered after I hooked up strace to actual apps
The primary app I hooked up strace to was Firefox, and it confirmed a steady cycle of epoll_wait, futex, and openat on /proc/self/maps. This indicated fixed internal-state checks between wake and sleep. With out strace, it will be arduous to consider that an idle browser can nonetheless concern a number of syscalls per second.
Attaching strace to apt confirmed me quite a bit about what occurs mid-install. By together with the -f flag, I may see every subprocess seem as a brand new PID. It was an fascinating course of: the guardian spawns a toddler through execve, the kid writes to /var/lib/dpkg/, and the following subprocess begins. My bundle set up immediately grew to become a visual chain of steps.
After weeks of utilizing strace, I’d advocate it for diagnosing hangs, file errors, and community failures. Nonetheless, as a result of it provides overhead, it is not excellent for manufacturing monitoring. I exploit it alongside widespread troubleshooting instruments, although it is not appropriate for steady manufacturing monitoring as a result of overhead.
OS
Linux
Minimal CPU Specs
64-bit Single-core
Minimal RAM Specs
1.5 GB
Linux Mint is a well-liked, free, and open-source working system for desktops and laptops. It’s user-friendly, secure, and practical out of the field.