I’ve seen too many consultants discuss DNS fixes or switching DNS suppliers for pace or privateness benefits. Whereas these might look like important modifications, they are often wasted and ineffective in case your browser is not utilizing the identical DNS as your system.
The browser’s DNS-over-HTTPS (DoH) function controls decision throughout the browser itself. With out fixing that one setting, your DNS modifications may not matter. Let me present you precisely why and the right way to repair it.
Examine this setting first earlier than altering the rest
Your browser could be resolving domains by means of a very totally different server
Fashionable browsers typically resolve DNS independently of the host, so settings that apply to the router and working system don’t at all times affect browser DNS.
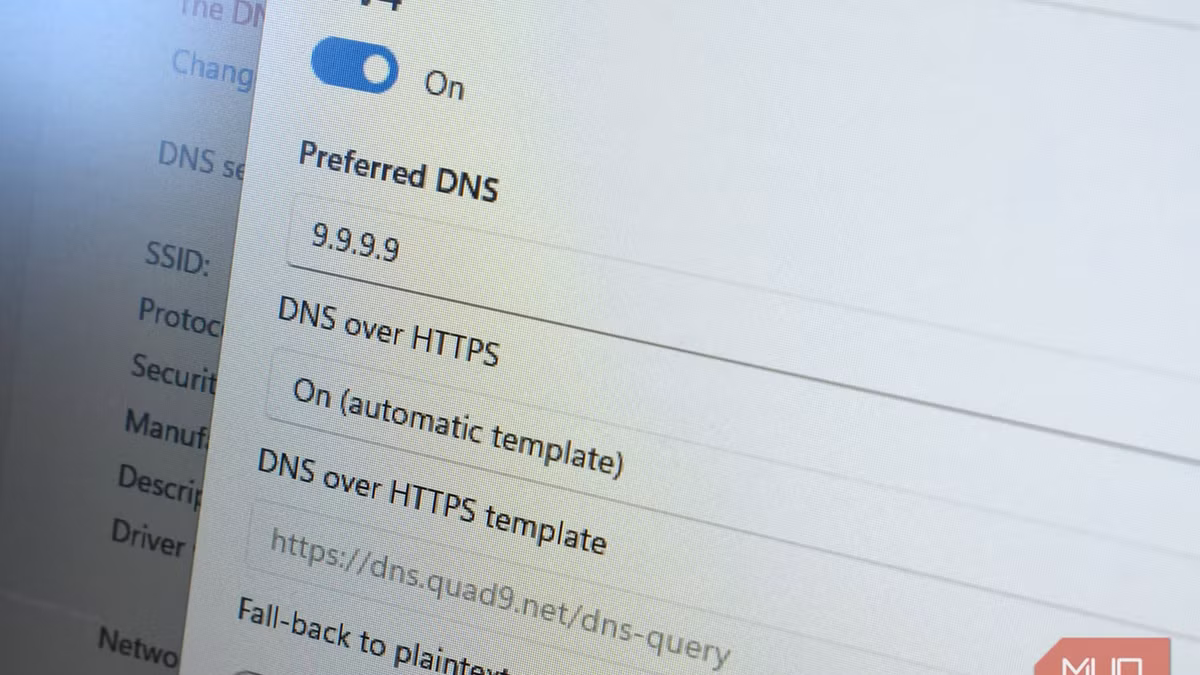
On Chrome, navigate to Settings -> Privateness and safety -> Safety, then choose Use safe DNS. If that is set to OS default (when out there), Chrome would not essentially swap to a unique supplier however tries updating the present DNS connection to an encrypted one. That is the default and deliberately conservative mode on Chrome that will get activated provided that your present DNS supplier helps DoH. With an area resolver similar to Pi-hole, Chrome defaults to your system DNS and would not override it. Edge is constructed on Chromium and behaves identical to Chrome.
With Firefox, there’s a actual override. Navigate to Settings -> Privateness & Safety -> DNS-over-HTTPS. Right here, it presents Off, Default Safety, Elevated Safety, and Max Safety modes. In case you use both Elevated Safety or Max Safety, Firefox will route queries by means of an exterior resolver—Cloudflare by default, although NextDNS can be out there — whatever the DNS the system makes use of.
You may verify this conduct by working Browserleaks’ DNS leak check with DoH enabled after which with DoH disabled. You will get affirmation that the browser has been overriding your DNS if the resolver modifications between the 2 checks.
Why browsers decided that impacts your total community
The privateness downside DoH was constructed to resolve — and the management it takes away
This conduct is intentional; the browser’s DNS layer was intentionally added to repair an actual vulnerability.
With conventional DNS, anybody between you and the DNS server can see your area lookups as a result of DNS queries are despatched in plain textual content. In sure conditions, these queries may be intercepted and redirected. DNS-over-HTTPS makes use of encrypted visitors to wrap queries in order that they give the impression of being an identical to your common net shopping visitors to anybody trying from the surface.
Nonetheless, DNS-over-HTTPS takes away DNS management from the community and provides it to the browser, which is why you could find yourself with totally different DNS settings for various components of your visitors.
DNS layer
What visitors it covers
Default managed by
Router DNS
All gadgets on the community
Your ISP, except you have modified it
System (OS) DNS
All apps on that machine
You, when you configure it
Browser DoH
Solely visitors inside that browser
The browser vendor
For the reason that browser’s DNS layer sits above the system and router layers, browser visitors might ignore DNS modifications made decrease down.
Associated
I ended utilizing browser VPNs after this—and you need to too
You need to keep away from browser VPNs for safety and efficiency causes.
When this setting breaks what you are attempting to do
Actual setups that cease working when browser DNS takes over
You usually discover DoH when one thing stops working as anticipated — normally as a result of a setup counting on network-level DNS is utilized in a browser that ignores it.
Pi-hole and network-wide advert blockers are sometimes affected as a result of browser DoH completely bypasses them if DNS filtering is carried out on the router stage. You will discover that the advertisements preserve loading on the browser, and you may marvel why it really works high quality for different apps on the identical community.
Parental management DNS companies are efficient at filtering DNS as a result of they intercept DNS queries earlier than they resolve. Nonetheless, the filters merely by no means see the queries if the browser sends them elsewhere.
The trade-off additionally applies to DNS filtering, which is an integral a part of company and college networks. You may encounter surprising entry points if the browser is routing round it.
Along with these, the browser’s exterior resolver will not have the wanted information when you usually entry inner addresses by hostname. Whereas all parts that usually require native DNS will preserve resolving in different apps, they merely won’t resolve contained in the browser.
The easy adjustment that makes your DNS setup behave as anticipated
You want all layers of the DNS to level in the identical path. That is the one means it really works predictably. The very steps you are taking will rely in your particular setup.
Here is what I do:
Your state of affairs
What to do
No particular setup (you simply need your DNS change to use)
Flip off browser DoH, or go away Chrome on computerized (it will not override)
Utilizing Pi-hole, OpenDNS, or any filtering DNS
Disable DoH within the browser (network-level filters have to see the question)
On public Wi-Fi with no VPN
Hold DoH on (it protects your queries from the community operator)
Utilizing a VPN
Disable browser DoH (the VPN already handles encrypted DNS)
On a piece or faculty community
Examine with IT, or disable DoH to keep away from bypassing community coverage
Need encryption but additionally need your customized DNS to use
Match the browser’s DoH supplier to your system DNS (e.g., each set to Cloudflare)
DoH should not be an issue; you solely need to convey it according to the opposite components of your setup. This manner, modifications to your DNS will persistently ship predictable conduct.